In last couple of years we can notice a huge increase of textual and graphics contents generated or setted by AI (the important thing is to be present and constant in some way in the social flows, AI simplifies this). This abundance of contents as well as their homogeneity in format make all information sort… Continue reading Value of Content in the AI Era
Author: Nicola Zago
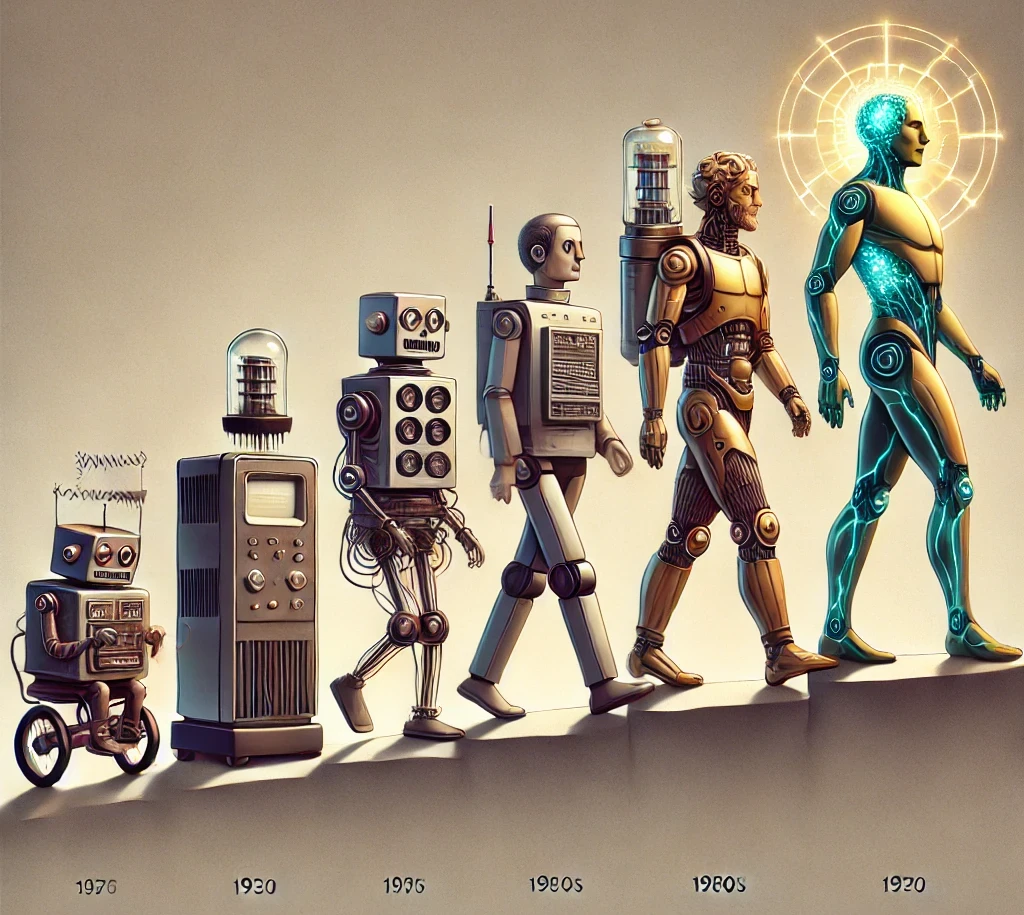
Artificial Intelligence – Part I: The Birth
Recently I have been invited to talk about history of AI and its current state of the art at UNIPOP, the “People’s University of Povegliano”, so I had the chance to delve into the origins and early stages of AI, which I had previously somewhat dismissed, despite having studied its developments from the 1980s onward… Continue reading Artificial Intelligence – Part I: The Birth
How to Recover Deleted Files with Linux using Sleuth Kit
I think that everyone has at least once delete a file that they shouldn’t have, either from a USB stick or from the recycle bin of their operating system, finding themselves in the unpleasant situation of no longer being able to undo the deletion. What not everyone knows is that this is an operation that… Continue reading How to Recover Deleted Files with Linux using Sleuth Kit
Magento 2.4.6 – Dynamic Properties are deprecated
The problem Dependency Injection (DI) is a core design pattern used extensively in Magento to manage class dependencies. In Magento, DI is implemented primarily through constructor injection, where dependencies are provided directly to class constructors rather than being instantiated within the class itself. There would be a lot of interesting things to say about this… Continue reading Magento 2.4.6 – Dynamic Properties are deprecated
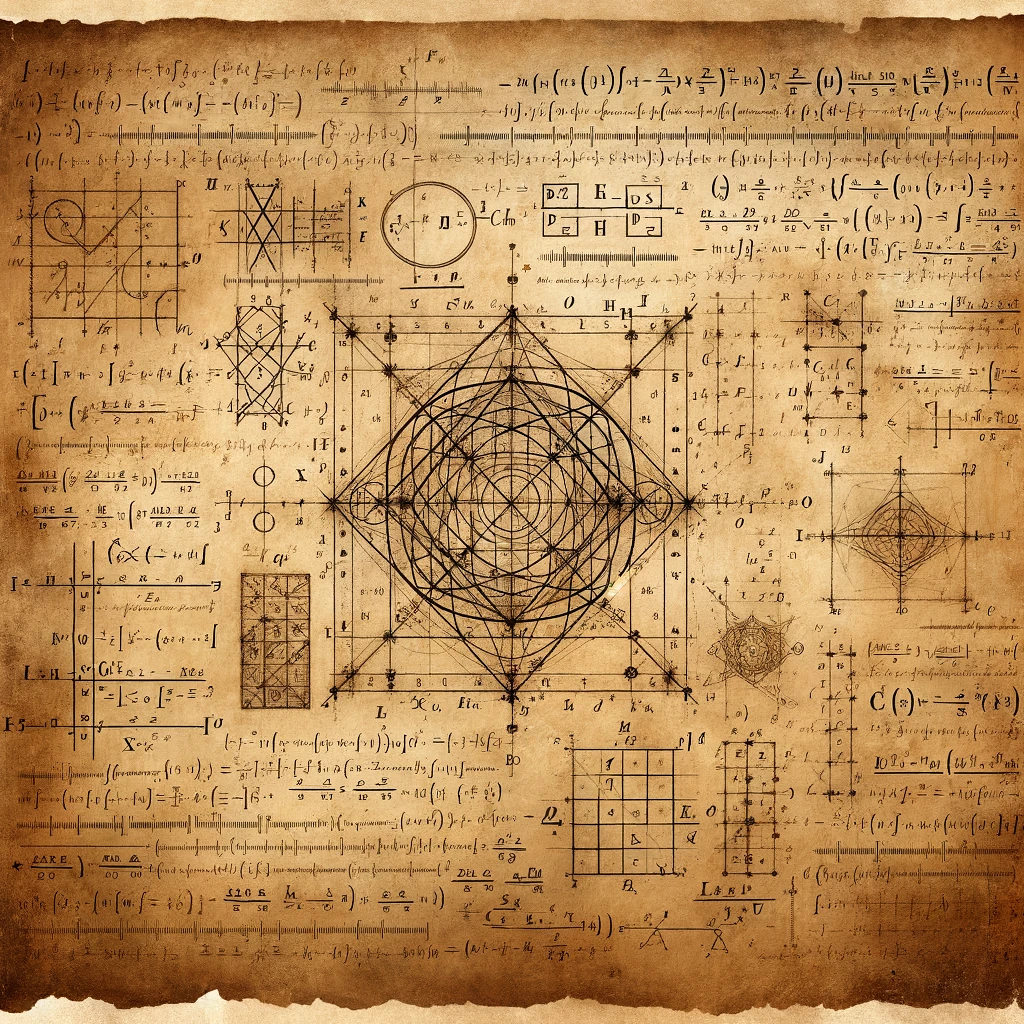
Challenging mathematical open problems
Over time I encountered a lot of interesting mathematical open problems that caught my attention. At some level I tried to understand and/or solve (in vain) them, but they remained in my mind and I hope at some point of my life to see their solution. The first two of these (Riemann Hypothesis and P… Continue reading Challenging mathematical open problems
Computational Models
Computers are very fast circuits able to do several basic logical, mathematical and memory operations and we use long sequences of these operations to perform almost every possible task. They are so fast that we think the elaboration as instantaneous, but if the input is large it may require some time. I still remember the… Continue reading Computational Models
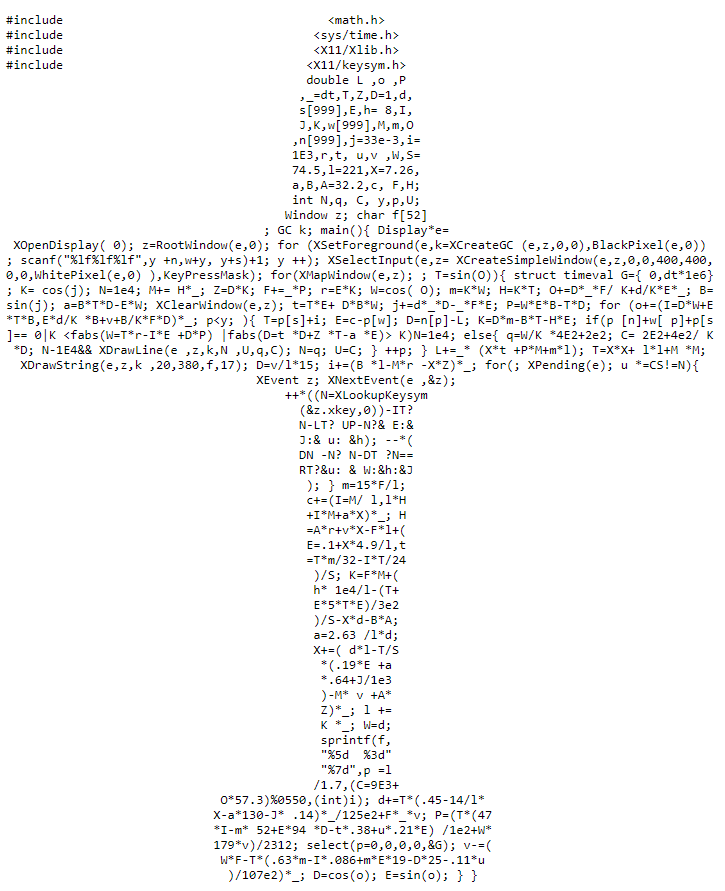
Obfuscation and IOCCC
In modern web programming languages an important concept is minimization of code, where the source code undergoes to a series of transformations (variables and functions are renamed, spaces and new lines removed and so on) in order reduce its size, compromising maintainability and readability in favor of space (and so speed of the download and… Continue reading Obfuscation and IOCCC
One million digits of Pi
Let continue the serie of computation of mathematical constants that we started with Euler Number. This time our target is π, the famous “3.14” ratio between circumference and diameter of a circle. Since out target is to compute one million digits in few minutes this post will use concept of code optimization. Like e, π… Continue reading One million digits of Pi
Mersenne Primes and Perfect Numbers
Primes are a fascinating group of integer numbers. They definition is short and clear (a prime number is a number that can be divided without remainder only by itself and 1), there are infinite primes and “quite frequent” (for number of n digits they are about n/(log n), so one number every log n is… Continue reading Mersenne Primes and Perfect Numbers
Computing 1 million digits of Euler’s Number
With this thread I start a new mathematical and computational branch: the art of computing decimals of particular mathematical constants. The first one will be e, the Euler’s number, about 2.7182818284, which is the base of exponential function ex, the only function equal to its derivative. Its inverse is the natural logarithm ln x, or… Continue reading Computing 1 million digits of Euler’s Number