In modern web programming languages an important concept is minimization of code, where the source code undergoes to a series of transformations (variables and functions are renamed, spaces and new lines removed and so on) in order reduce its size, compromising maintainability and readability in favor of space (and so speed of the download and parsing of the code).
Minimization has some aspects related to compression (eg. you can rename the most used variables/functions with names with a one letter name, and less used with a two or more letters name, more or less like in Huffman codes).
A related scope is obfuscation: when programming something it is preferable to make the code difficult to be understood and reused by others. This is particularly true in modern web technologies, where JavaScript executes client side, but it is valid also for Android Apps, that can be easily extracted and decompiled, or any programs that can somehow be reverted to code by its binary.
Obfuscation examples
Minimization, especially when replace variables and functions names, is already a form of lite obfuscation but it is only a side effect. Obfuscation uses a number of techniques that aim to make the code un-understandable also at cost of not being optimal for minimization, like:
- strings encryption, maybe string converted in base64, or containing hexadecimal codes of characters, or again converted in array ASCII codes. For example “text” can become:
- “dGV4dA==”: transformed in base64, in js it is
btoa('text') - [116, 101, 120, 116]: transformed in a array with ASCII code of character, using
str.charCodeAt(i)on single characters - “0x74657874”: transformed in a string with ASCII hexadecimal code of character, for example using
str.charCodeAt(i).toString(16).toUpperCase()on single characters
- “dGV4dA==”: transformed in base64, in js it is
- variables and functions renaming: not only the renaming used by minimization, imagine a code where variables and functions names are changed and encrypted like strings in previous point.
- adding dead code: the insertion of pieces of code never called of that do nothing add complexity in the understanding of code (remember that give more information that necessary often is misleading)
- code transposition: a rearrangement of code that preserve the execution order of statement but scramble the traditional logical code grouping. Just to give an example, imagine to take the statements of a function, transform them in strings encoded with different techniques, put them in more arrays in a random order, executing them using eval() in a function.
These are just some possible ways to obfuscate codes, the list can be easily extended. Online you can find a lot of obfuscation and deobfuscation tools (deobfuscate.io) or libraries (obfuscator.io) thought to be used also directly in your projects to encode the bundles produced. Here I listed tools for js but there are tools for a lot of other languages.
IOCCC
The International Obfuscated C Code Contest is a contest where obfuscated C programs are evaluated by creativity.
I randomly found it almost 20 years ago will searching for info about this 158 characters C program that computes 2400 digits of Greek Pi (I only recently understand it thanks to ChatGPT, it uses Spigot algorithm for Pi):
main(){int a=1e4,c=3e3,b=c,d=0,e=0,f[3000],g=1,h=0;
for(;b;!--b?printf("%04d",e+d/a),e=d%a,h=b=c-=15:f[b]=
(d=d/g*b+a*(h?f[b]:2e3))%(g=b*2-1));}
The programs participating to the contest don’t even seem syntactically valid and are ofter presented as ASCII art, but surprisingly they do incredible things. For example in the 1998 contest the following code has been presented:
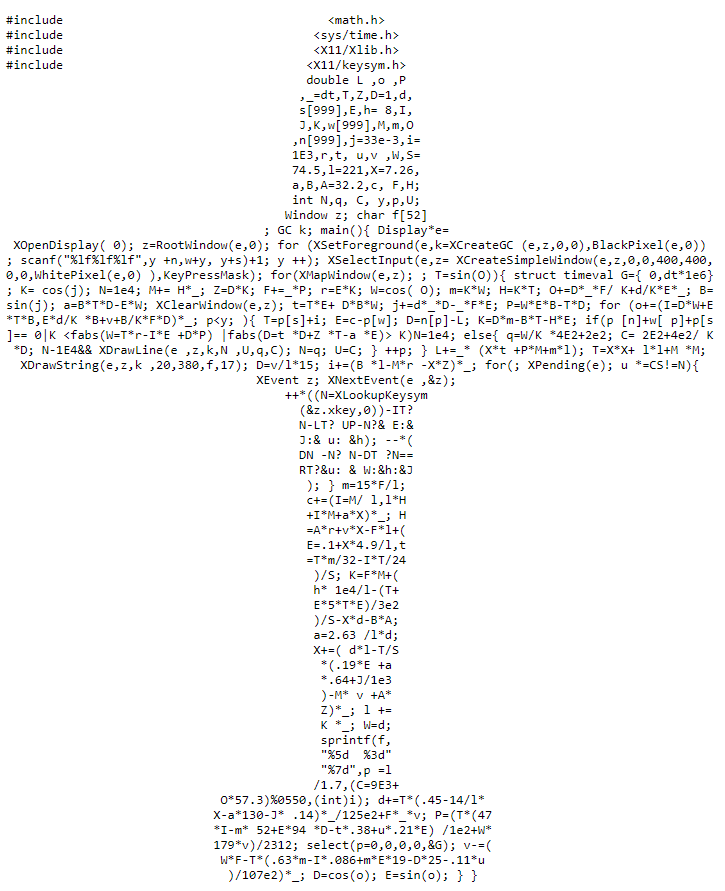
Here the textual entry: https://www.ioccc.org/1998/banks.c
This is a 3d flight simulator in just 2256 bytes, it takes in input files with coordinates of landscapes and allows you to fly in it with keyboard keys. You need a Linux X environment to try it.
There are a lot of IOCCC editions available to be tried and studied, some of them are very inspiring.
I’ll try to update this article putting a selection of them (I remember beautiful textual animations) but I suggest you to visit the official site and explore it by yourself.